netsec - Network Security
 www.buskill.in
www.buskill.in
Today we're ecstatic to [publish our first demo](https://www.buskill.in/3d-print-2024-05/) showing a homemade BusKill Cable (in the prototype 3D-printed case) triggering a lockscreen. | [](https://www.buskill.in/3d-print-2024-05/) | |:--:| | *Watch the [3D-Printed USB Dead Man Switch (Prototype Demo)](https://www.youtube.com/v/vFTQatw94VU) for more info [youtube.com/v/vFTQatw94VU](https://www.youtube.com/v/vFTQatw94VU)* | via [@Goldfishlaser@lemmy.ml](https://lemmy.ml/u/Goldfishlaser) In our [last update](https://www.buskill.in/3d-print-2023-08/), I showed a video demo where I successfully triggered a lockscreen using a BusKill prototype without the 3D-printed body for the case and N35 disc magnets. I realized that the N35 disc magnets were not strong enough. In this update, I show a demo with the prototype built inside a 3D-printed case and with (stronger) N42 and N52 cube magnets. # What is BusKill? BusKill is a laptop kill-cord. It's a USB cable with a magnetic breakaway that you attach to your body and connect to your computer. | [](https://www.buskill.in/#demo) | |:--:| | *Watch the [BusKill Explainer Video](https://www.buskill.in/#demo) for more info [youtube.com/v/qPwyoD_cQR4](https://www.youtube.com/v/qPwyoD_cQR4)* | If the connection between you to your computer is severed, then your device will lock, shutdown, or shred its encryption keys -- thus keeping your encrypted data safe from thieves that steal your device. # Why? While [we do what we can](https://www.buskill.in//buskill-onion-service-tor/) to allow at-risk folks to [purchase BusKill cables anonymously](https://www.buskill.in//bitcoin-black-friday-2023/#privacy), there is always the risk of [interdiction](https://docs.buskill.in/buskill-app/en/stable/faq.html#q-what-about-interdiction). We don't consider hologram stickers or tamper-evident tape/crisps/glitter to be sufficient solutions to supply-chain security. Rather, the solution to these attacks is to build open-source, easily inspectable hardware whose integrity can be validated without damaging the device and without sophisticated technology. Actually, the best way to confirm the integrity of your hardware is to build it yourself. Fortunately, BusKill doesn't have any circuit boards, microcontrollers, or silicon; it's trivial to print your own BusKill cable -- which is essentially a USB extension cable with a magnetic breakaway in the middle Mitigating interdiction via 3D printing is one of many reasons that [Melanie Allen](https://github.com/Goldfishlaser) has been diligently working on prototyping a 3D-printable BusKill cable this year. In this article, we hope to showcase her progress and provide you with some OpenSCAD and `.stl` files you can use to build your own version of the prototype, if you want to help us test and improve the design. # Print BusKill [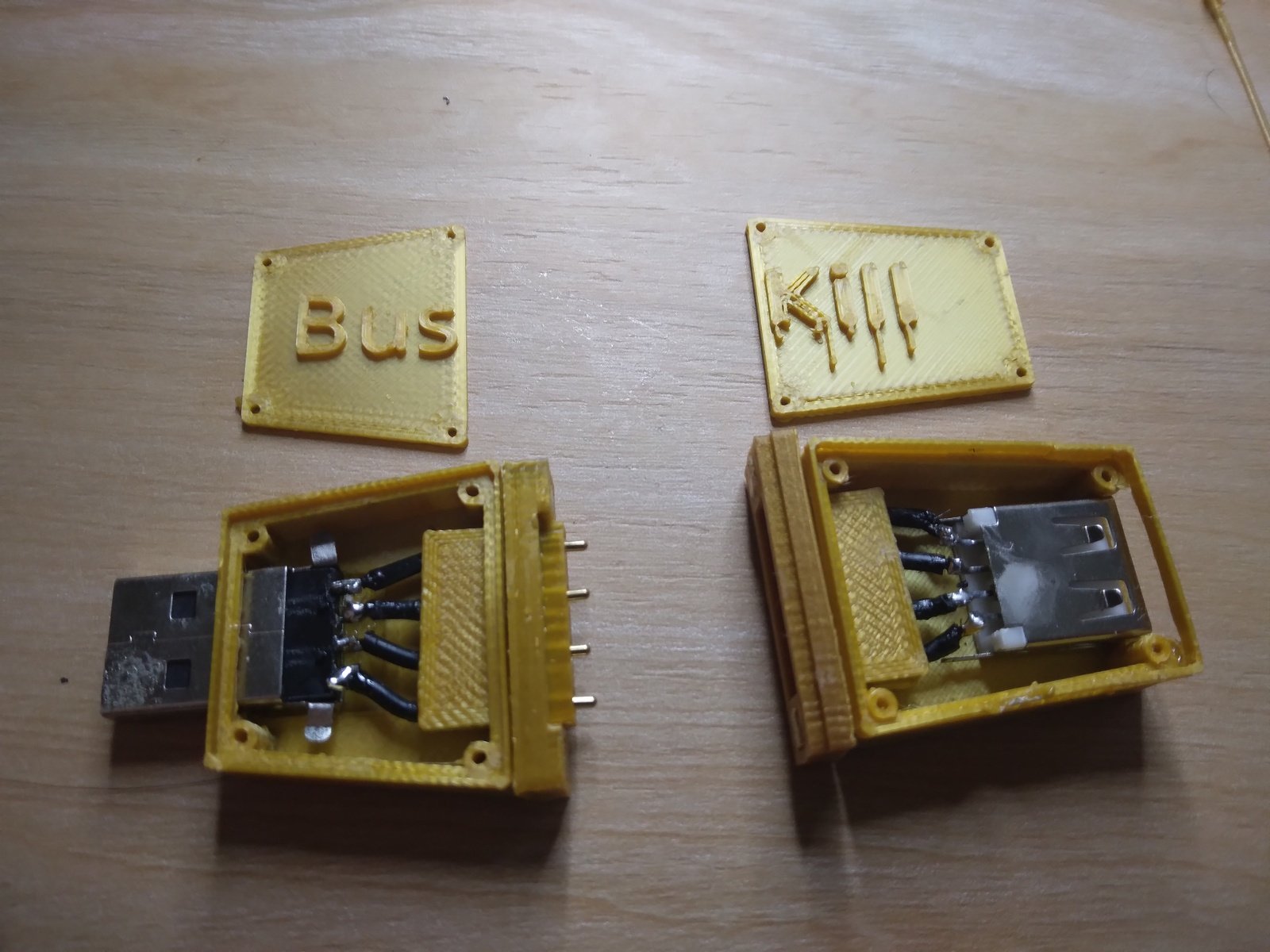](https://www.buskill.in/3d-print-2024-05/) If you'd like to reproduce our experiment and print your own BusKill cable prototype, you can [download the stl files](https://www.buskill.in/3d-print-2024-05/) and [read our instructions](https://www.buskill.in/3d-print-2024-05/) here: * [buskill.in/3d-print-2024-05](https://www.buskill.in/3d-print-2024-05/) # Iterate with us! **If you have access to a 3D Printer, you have basic EE experience, or you'd like to help us test our 3D printable BusKill prototype, please** [let us know](https://buskill.in/contact). The whole is greater than the sum of its parts, and we're eager to finish-off this 3D printable BusKill prototype to help make this security-critical tool accessible to more people world-wide!
 buskill.in
buskill.in
In celebration of **Bitcoin Black Friday 2023**, we're offering a **10% discount** on all [BusKill cables](https://buskill.in/buy/) sold between Nov 18 to Dec 03. | [](https://buskill.in/bitcoin-black-friday-2023) | |:--:| | *BusKill [Bitcoin Black Friday Sale](https://buskill.in/bitcoin-black-friday-2023) - Our Dead Man Switch Magnetic USB Breakaway cables are [10% off](https://buskill.in/buy/) all orders paid with cryptocurrency* | # What is BusKill? BusKill is a laptop kill-cord. It's a USB cable with a magnetic breakaway that you attach to your body and connect to your computer. | [](https://www.buskill.in/#demo) | |:--:| | *Watch the [BusKill Explainer Video](https://www.buskill.in/#demo) for more info [youtube.com/v/qPwyoD_cQR4](https://www.youtube.com/v/qPwyoD_cQR4)* | If the connection between you to your computer is severed, then your device will lock, shutdown, or shred its encryption keys -- thus keeping your encrypted data safe from thieves that steal your device. # What is Bitcoin Black Friday? [Black Friday](https://en.wikipedia.org/wiki/Black_Friday_(shopping)) is ~1 month before Christmas, and it's the busiest shopping day in the US. The first "[Bitcoin Friday](https://web.archive.org/web/20121213223642/http://bitcoinfriday.com/)" ([launched](https://bitcoinmagazine.com/culture/bitcoin-friday-sale-happening-today-1352497394) by Jon Holmquist) was [Nov 9th, 2012](https://www.theregister.com/2012/11/09/bitcoin_friday_sale_event/) (at the time, one bitcoin was ~$11). The following year, the two ideas merged to become [Bitcoin Black Friday](https://www.vice.com/en/article/jp5xxp/bitcoin-is-taking-on-black-friday). This year, we're joining Bitcoin Black Friday by offering our products at a 10% discount if you pay with cryptocurrency. # Why should I use cryptocurrencies? We've always accepted cryptocurrencies because: 1. They're more [secure](https://www.buskill.in/bitcoin-black-friday-2023/#secure) than pre-cryptocurrency payment methods 2. They're a more [egalitarian](https://www.buskill.in/bitcoin-black-friday-2023/#egalitarian) system than pre-cryptocurrency finance 3. They're more [environmentally friendly](https://www.buskill.in/bitcoin-black-friday-2023/#environmentalism) than pre-cryptocurrency financial systems 4. The [fees are less](https://www.buskill.in/bitcoin-black-friday-2023/#fees) than pre-cryptocurrency transactions 5. They allow for [anonymous](https://www.buskill.in/bitcoin-black-friday-2023/#privacy) purchases online 6. Their transactions are [censorship-resistant](https://www.buskill.in/bitcoin-black-friday-2023/#censorship) ## Security Before cryptocurrencies, making an online transaction was horrendously insecure and backwards. | [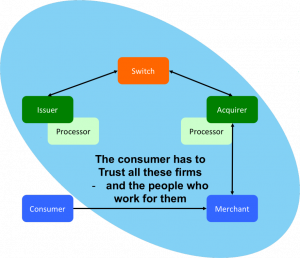](https://buskill.in/bitcoin-black-friday-2023) | |:--:| | "Conceptually, pull-based transactions are really not that different than giving three parties the password to your online banking service and trusting them to log in and take what they need. You have to trust the merchant, their IT supplier; the acquiring bank, their third-party processor; the card network; and your own card issuer---and everybody who works for them and has access to their systems. If a bad guy gets hold of your card details at any point in this process, they could drain your account. | | The picture shows the scope of all the entities with access to your critical card information" [source](https://www.coincenter.org/education/crypto-regulation-faq/how-are-payments-with-bitcoin-different-than-credit-cards/) | [Asymmetric cryptography](https://en.wikipedia.org/wiki/Public-key_cryptography#History) has been available since the 1970s, but [CNP (Card Not Present)](https://en.wikipedia.org/wiki/Card_not_present_transaction%22) transactions to this day still don't use public keys to sign transactions. Rather, you give your private keys (that is, your credit card number, expiry, etc) directly to the merchant and you authorize them to **pull money out of your account** (trusting that they take the right amount and not to loose those precious credentials). Bitcoin flipped this around to actually make transactions secure. **With bitcoin**, you don't give others the keys to take money out of your account. Instead, **transactions are push-based**. You sign a transaction with your private keys, and those keys are shared with no-one. Even today, pre-cryptocurrency transactions are abhorrently insecure. In the US or Europe, if someone knows your account number and bank, they can [direct debit money out of your account](https://www.telegraph.co.uk/news/uknews/1574781/Jeremy-Clarkson-eats-his-words-over-ID-theft.html). For the same reason, losses due to credit card theft is enormous. To quote Satoshi Nakamoto's criticism of pre-cryptocurrency transactions, "A certain percentage of fraud is accepted as unavoidable" In fact, fraudulent transactions in the banking industry are so common that your bank will generally reimburse your account for any malicious transactions that you tell them about within 60-90 days. But if someone drains your account of all your money and you don't notice for 12 months? Too bad. All your money is gone. | [](https://buskill.in/bitcoin-black-friday-2023) | |:--:| | In Bitcoin, transactions are push-based. [source](https://www.coincenter.org/education/crypto-regulation-faq/how-are-payments-with-bitcoin-different-than-credit-cards/) | [Tokenization](https://en.wikipedia.org/wiki/Tokenization_(data_security)) and [3DS](https://en.wikipedia.org/wiki/3-D_Secure) are merely bandages on a fundamentally backwards, pull-based transaction model. But because [bitcoin is push-based](https://www.coincenter.org/education/crypto-regulation-faq/how-are-payments-with-bitcoin-different-than-credit-cards/), it's magnitudes more secure. ## Egalitarian If you have a bank account, then you probably take a lot of things for granted. Like buying things online (with a credit card). Or getting cash when traveling abroad (from an ATM machine). Or taking out a loan so you can start a business. Before crypto-currencies, it was very difficult to do these things unless you had a bank account. And in 2008 (the year with the first-ever bitcoin transaction), McKinsey & Company published a report concluding that [half of the world's adult population is unbanked](https://www.mckinsey.com/~/media/mckinsey/industries/public%20and%20social%20sector/our%20insights/half%20the%20world%20is%20unbanked/half-the-world-is-unbanked.pdf). But with crypto-currencies, anyone with access to the internet and a computer or smart phone can use bitcoin to send and receive money online -- without needing to first obtain a bank account. ## Environmentalism The energy required to facilitate transactions in decentralized, blockchain-based cryptocurrencies like bitcoin is minuscule by comparison. And, most importantly, the amount of energy used to solve the proof-of-work problem does not grow as the number of transactions-per-second grows. Traditional financial institutions require an enormous amount of overhead to facilitate transactions in their centralized networks. Unlike bitcoin, which was designed specifically to [eliminate the unnecessary overhead](https://www.buskill.in/bitcoin-black-friday-2023/#fees) created by a trusted third party, pre-cryptocurrency transactions required humans to verify transactions. These humans require office buildings. These office buildings require energy to build and maintain. And, most importantly, as the number of transactions-per-second grows on their network, the number of humans and office space also grows. | [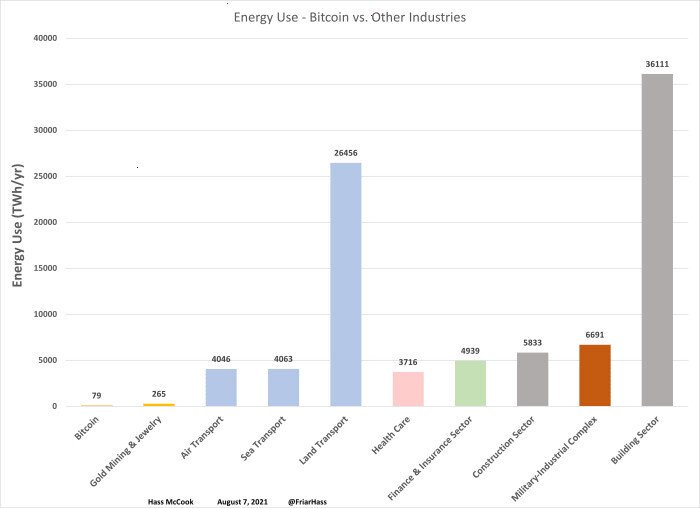](https://buskill.in/bitcoin-black-friday-2023/) | |:--:| | Bitcoin versus other industries --- yearly energy use, in TWh [source](https://bitcoinmagazine.com/business/bitcoin-energy-use-compare-industry) | This fact is often misunderstood because there's a lot of misinformation on the Internet that makes a few disingenuous modifications to the facts: 1. They calculate the energy usage of the computers processing transactions only, maliciously omitting calculating the energy usage of the entire industry's infrastructure (eg energy used by office buildings) 2. They calculate the energy usage *per transaction*, maliciously omitting the fact that the amount of energy expended by bitcoin miners is automatically adjusted by the proof-of-work algorithm (so energy usage does not increase as the network scales-up) 3. They offer statistics about "energy usage" without mentioning the energy sources. It matters if the energy source is coal/nuclear/natural-gas or solar/wind/hydroelectric > | "...estimates for what percentage of Bitcoin mining uses renewable energy vary widely. In December 2019, one report suggested that 73% of Bitcoin's energy consumption was carbon neutral, largely due to the abundance of hydro power in major mining hubs such as Southwest China and Scandinavia. On the other hand, the CCAF estimated in September 2020 that the figure is closer to 39%. But even if the lower number is correct, that's still **almost twice as much [renewable energy sources] as the U.S. grid**" | [](https://buskill.in/bitcoin-black-friday-2023/) | > |:--:|:--:| > | [source: Harvard Business Review](https://hbr.org/2021/05/how-much-energy-does-bitcoin-actually-consume) | Nic Carter | The facts are that the energy usage of bitcoin is magnitudes less than the energy used by pre-cryptocurrency financial intuitions, that energy usage does not increase as the number of transactions processed by the network increases, and that mining bitcoin is often done with renewable energy. The facts are that the energy usage of bitcoin is magnitudes less than the energy used by pre-cryptocurrency financial intuitions, that energy usage does not increase as the number of transactions processed by the network increases, and that mining bitcoin is often done with renewable energy. ## Low Fees The introduction to the [Bitcoin White Paper](https://bitcoin.org/bitcoin.pdf) (2008) clearly states that Bitcoin was created to reduce costs by using a distributed ledger (the blockchain) to eliminate the need for a trusted third party. > | "Commerce on the Internet has come to rely almost exclusively on financial institutions serving as trusted third parties to process electronic payments. While the system works well enough for most transactions, it still suffers from the inherent weaknesses of the trust based model. | | > |:---|:---| > | Completely non-reversible transactions are not really possible, since financial institutions cannot avoid mediating disputes. **The cost of mediation increases transaction costs**... | | > | These costs and payment uncertainties can be avoided in person by using physical currency, but no mechanism exists to make payments over a communications channel without a trusted party. | | > | What is needed is an electronic payment system based on cryptographic proof instead of trust, allowing any two willing parties to transact directly with each other without the need for a trusted third party. Transactions that are computationally impractical to reverse would protect sellers from fraud, and routine escrow mechanisms could easily be implemented to protect buyers. In this paper, we propose a solution to the double-spending problem using a peer-to-peer distributed timestamp server to generate computational proof of the chronological order of transactions." | [](https://buskill.in/bitcoin-black-friday-2023/) | > | [source: Bitcoin Whitepaper](https://bitcoin.org/bitcoin.pdf) | Satoshi Nakamoto | At the time of writing, **the [average transaction fee](https://bitcoinfees.net/) for a bitcoin transaction is $0.06**. And unlike pre-cryptocurrency transactions, you can increase or decrease the fee that you pay to increase or decrease the time it takes for the transaction to complete (at $0.06, it will get added to the blockchain in **~1 hour**). By comparison, the way to send funds internationally through the Internet via pre-cryptocurrency banks is via an **[international wire transfer](https://en.wikipedia.org/wiki/Wire_transfer)**. Fees very per bank, but [they typically charge **$15-$85 per transaction**](https://www.nerdwallet.com/article/banking/wire-transfers-what-banks-charge). And unlike bitcoin, wire transfers won't make move on nights and weekends, so they can take **1-7 days** to complete. Also, with bitcoin, that $0.06 transaction fee only applies when you're sending money. Many banks will *also* charge a fee for an incoming wire transfer. In bitcoin, there is no transaction fee to receive money. ## Anonymity Though early cryptocurrencies like Bitcoin don't ensure anonymity like newer privacy coins, [ZCash](https://en.wikipedia.org/wiki/Zcash) and [Monero](https://en.wikipedia.org/wiki/Monero) were designed specifically to provide private transactions. This allows our customers to purchase from us anonymously, which can be extremely important for activists and journalists whose lives are threatened by their adversaries. | [](https://twitter.com/wikileaks/status/80774521350668288) | |:--:| | WikiLeaks started accepting donations in Bitcoin 7 months after PayPal froze their account | We accept both ZCash and Monero. If you'd like us to accept another privacy coin, please [contact us](https://buskill.in/contact) :) ## Censorship-Resistant Cryptocurrencies like bitcoin are peer-to-peer and permissionless. Transactions exchanging bitcoins occur directly between two parties. There is **no middle-man** that has the power to block, freeze, or reverse transactions. Before blockchains were used to maintain a public ledger and enable peer-to-peer transactions, we were dependent on big financial institutions to move money on our behalf through the internet. That antiquated system allowed them to censor transactions, such as donations made to media outlets reporting war crimes and donations to protest movements. > | "For me, that is one of the coolest things about bitcoin... | | > |:---|:---| > | People can potentially use it donate more anonymously to dissident groups and causes in a world where mass government surveillance threatens freedom of expression and certainly harms activists' ability to fundraise for their work, when people are afraid they could be targeted by a government for donating to a worthy cause." | [](https://buskill.in/bitcoin-black-friday-2023/) | > | [source](https://www.vice.com/en/article/jp5xxp/bitcoin-is-taking-on-black-friday) | Evan Greer | After [PayPal froze WikiLeaks's donation account](https://wikileaks.org/PayPal-freezes-WikiLeaks-donations.html) in 2010, WikiLeaks started [accepting bicoin](https://www.forbes.com/sites/forbesdigitalcovers/2018/07/30/the-backsies-billionaire-texan-builds-second-fortune-from-wreckage-of-real-estate-empire-hed-sold/?sh=6f75c6883a72) in 2011. From [Occupy Wall Street](https://web.archive.org/web/20111126164538/http://occupywallst.org/donate/) to [Ukraine](https://www.washingtonpost.com/world/2022/03/03/donate-ukraine-money-crypto/), defenders of democracy have utilized permissionless cryptocurrencies to accept international donations without the risk of transactions made through financial institutions. ## Buy BusKill with crypto Don't risk loosing your crypto to a thief that steals your laptop. Get your own [BusKill Cable](https://buskill.in/buy/) at a 10% discount today! **[Buy a BusKill Cable](https://buskill.in/buy)** [https://buskill.in/buy](https://buskill.in/buy) You can also buy a BusKill cable with bitcoin, monero, and other altcoins from our [BusKill Store's .onion site](http://buskillvampfih2iucxhit3qp36i2zzql3u6pmkeafvlxs3tlmot5yad.onion/buy/). ` ` [](https://buskill.in/buy) [](https://buskill.in/buy) ` ` ` ` Stay safe, The BusKill Team https://www.buskill.in/ http://www.buskillvampfih2iucxhit3qp36i2zzql3u6pmkeafvlxs3tlmot5yad.onion
 www.buskill.in
www.buskill.in
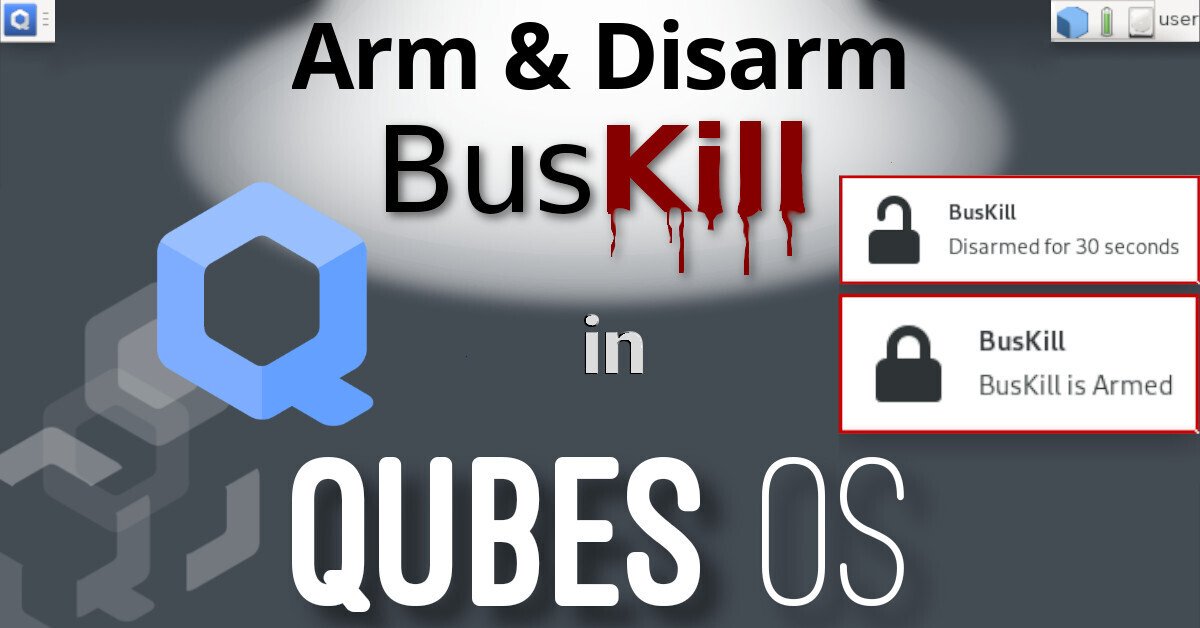
This article describes how to setup keyboard shortcuts in QubesOS so that you can temporarily disarm (pause) the BusKill laptop kill cord. This allows the user to, for example, go to the bathroom without causing their computer to shutdown or self-destruct. [](https://buskill.in/qubes-disarm) This is a guide that builds on part one: [A Laptop Kill Cord for QubesOS (1/2)](/qubes-os/). Before reading this, you should already be familiar with how to [setup udev rules for BusKill on QubesOS](https://www.buskill.in/qubes-os/). 1. [A Laptop Kill Cord for QubesOS (1/2)](/qubes-os/) 2. Disarm BusKill in QubesOS (2/2) > ⓘ Note: This post is adapted from its original [article on Tom > Hocker\'s blog](https://humandecoded.io/qubes-os-yubikey-buskill/). # What is BusKill? > What if someone literally steals your laptop while you\'re working > with classified information inside a Whonix DispVM? They\'d also be > able to recover data from previous DispVMs\--as Disposable VM\'s > rootfs virtual files are *not* securely shredded after your DispVM is > destroyed. Are you a security researcher, journalist, or intelligence operative that works in QubesOS\--exploiting Qubes\' [brilliant security-through-compartimentalization](https://freedom.press/news/the-operating-system-that-can-protect-you-even-if-you-get-hacked/) to keep your data safe? Do you make use of Whonix [Disposable VMs](https://www.qubes-os.org/doc/disposablevm/) for your work? Great! This post is for you. I\'m sure your QubesOS laptop has Full Disk Encryption and you\'re using a strong passphrase. But what if someone literally steals your laptop while you\'re working with classified information inside a Whonix DispVM? Not only will they get access to all of your AppVM\'s private data and the currently-running Whonix DispVM\'s data, but there\'s a high chance they\'d be able to recover data from [previous DispVMs](https://www.whonix.org/wiki/Qubes/DisposableVM#Warnings)\--as **Disposable VM\'s rootfs virtual files ([volatile.img](https://groups.google.com/forum/#!topic/qubes-devel/QwL5PjqPs-4/discussion)) are [*not* securely shredded](https://github.com/QubesOS/qubes-issues/issues/904) after your DispVM is destroyed** by Qubes! Let\'s say you\'re a journalist, activist, whistleblower, or a human rights worker in an oppressive regime. Or an intelligence operative behind enemy lines doing research or preparing a top-secret document behind a locked door. What do you do to protect your data, sources, or assets when the secret police suddenly batter down your door? How quickly can you *actually* act to shutdown your laptop and shred your RAM and/or FDE encryption keys? | [](https://www.buskill.in/#demo) | |:--:| | *Watch the [BusKill Explainer Video](https://www.buskill.in/#demo) for more info [youtube.com/v/qPwyoD_cQR4](https://www.youtube.com/v/qPwyoD_cQR4)* | BusKill utilizes a magnetic trip-wire that tethers your body to your laptop. If you suddenly jump to your feet or fall off your chair (in response to the battering ram crashing through your door) or your laptop is ripped off your table by a group of armed thugs, the data bus\' magnetic connection will be severed. This event causes a configurable *trigger* to execute. The BusKill `trigger` can be anything from: 1. locking your screen or 2. shutting down the computer or 3. initiating a [self-destruct](/luks-self-destruct/) sequence While our [last post](qubes-os) described how to setup such a system in QubesOS with BusKill, *this* post will describe how to add keyboard shortcuts to arm & disarm the dead man switch (eg so you can go to the bathroom). # Disclaimer This guide contains experimental files, commands, and software. The information contained in this article may or may not lead to corruption or total permanent deletion of some or all of your data. We\'ve done our best to carefully guide the user so they know the risks of each BusKill trigger, but we cannot be responsible for any data loss that has occurred as a result of following this guide. The contents of this guide is provided openly and is licensed under the [CC-BY-SA](https://creativecommons.org/licenses/by-sa/4.0/) license. The software included in this guide is licensed under the [GNU GPLv3](https://www.gnu.org/licenses/gpl-3.0.html) license. All content here is consistent with the limitations of liabilities outlined in its respective licenses. We highly recommend that any experiments with the scripts included in this article are used exclusively on a disposable machine containing no valuable data. If data loss is a concern for you, then leave now and do not proceed with following this guide. You have been warned. ## Release Note Also be aware that, due to the risks outlined above, BusKill will *not* be released with this \"self-destruct\" trigger. If you [purchase](/buy) a BusKill cable, it will only ship with non-destructive triggers that lock the screen or shutdown the computer. Advanced users can follow guides to add additional destructive triggers, such as the one described in this post, but they should do so at their own risk\--taking carefully into consideration all of the warnings outlined above and throughout this article. **Again, if you [buy](/buy) a BusKill cable, the worst that can happen is your computer will abruptly shutdown.** # Assumptions This guide necessarily makes several assumptions outlined below. ## sys-usb In this guide, we assume that your QubesOS install has a [USB-Qube](https://www.qubes-os.org/doc/usb-qubes/) named \'`sys-usb`\' for handling [USB events](https://www.qubes-os.org/doc/usb-devices/) on behalf of `dom0`. If you decided to combine your USB and networking Qubes at [install time](https://www.qubes-os.org/doc/installation-guide/#initial-setup), then replace all references in this guide for \'`sys-usb`\' to \'`sys-net`\'. If you decided to run your \'`sys-usb`\' VM as a DispoableVM at [install time](https://github.com/QubesOS/qubes-issues/issues/6684#issuecomment-1435381919), then replace all references in this guide for \'`sys-usb`\' its Disposable TemplateVM (eg \'`fedora-36-dvm`\'). ..And if you chose not to isolate your USB devices, then [may god help you](https://blog.invisiblethings.org/2011/05/31/usb-security-challenges.html). ## Udev Device Matching BusKill in Linux uses [udev](https://en.wikipedia.org/wiki/Udev) to detect when the USB\'s cable is severed. The exact udev rule that you use in the files below will depend on the drive you choose to use in your BusKill cable. In this guide, we identify our BusKill-specific drive with the \'`ENV{ID_MODEL}=="Micromax_A74"`\' [udev property](https://wiki.archlinux.org/index.php/Udev#udev_rule_example). You should replace this property with one that matches your BusKill-specific drive. To determine how to query your USB drive for device-specific identifiers, see [Introducing BusKill: A Kill Cord for your Laptop](/buskill-laptop-kill-cord-dead-man-switch/#software). Note that the \``udevadm monitor --environment --udev`\` command should be run in the \'`sys-usb`\' Qube. > ⓘ Note: If you\'d prefer to buy a BusKill cable than make your own, > you can buy one fully assembled [here](/buy). ## QubesOS Version This guide was written for QubesOS v4.1. ``` [user@dom0 ~]$ cat /etc/redhat-release Qubes release 4.1.2 (R4.1) [user@dom0 ~]$ ``` # BusKill Files This section will describe what files should be created and where. Due to the design of QubesOS, it takes a bit of mental gymnastics to understand what we\'re doing and why. It\'s important to keep in mind that, in QubesOS 1. The keyboard and UI are configured in \'`dom0'` 2. USB devices (like the BusKill device) are routed to the \'`sys-usb`\' VM 3. dom0 has the privilege to execute scripts inside other VMs (eg \'`sys-usb`\') 4. By design, VMs should \*not\* be able to send arbitrary commands to be executed in dom0 5. \...but via the [qubes-rpc](https://www.qubes-os.org/doc/qrexec/#qubes-rpc-services), we *can* permit some VMs (eg \'`sys-usb`\') to execute a script in dom0 (though for security reasons, ideally such that no data/input is sent from the less-trusted VM to dom0 \-- other than the name of the script) Due to the constraints listed above: 1. We\'ll be configuring the disarm button as keyboard shortcut in dom0 2. We\'ll be saving and executing the \'`buskill-disarm.sh`\' script in \'`sys-usb`\' (because these scripts manipulate our udev rules) 3. The keyboard shortcut in dom0 will *actually* be executing the above script in \'`sys-usb`\' ## sys-usb If you followed our [previous guide to setting-up BusKill in QubesOS](/qubes-os/), then you should already have a file in \'`sys-usb`\' at \'`/rw/config/buskill.rules`\'. You may even have modified it to trigger a [LUKS Self-Destruct](/luks-self-destruct/) on removal of your BusKill device. Because you\'re *now* experimenting with a new setup, let\'s go ahead and wipe out that old file with a new one that *just* executes a soft-shutdown. You might need some days to get used to the new disarm procedure, and you probably don\'t want to suddenly loose all your data due to an accidental false-positive! Execute the following on your \'`sys-usb`\' Qube: ``` mv /rw/config/buskill.rules /rw/config/buskill.rules.bak.`date "+%Y%m%d_%H%M%S"` cat << EOF | sudo tee /rw/config/buskill.rules ################################################################################ # File: sys-usb:/etc/udev/rules.d/buskill.rules -> /rw/config/buskill.rules # Purpose: Add buskill rules. For more info, see: https://buskill.in/qubes-os/ # Authors: Michael Altfield # Created: 2020-01-02 # License: GNU GPLv3 ################################################################################ ACTION=="remove", SUBSYSTEM=="usb", ENV{ID_MODEL}=="Micromax_A74", RUN+="/usr/bin/qrexec-client-vm dom0 buskill.softShutdown" EOF sudo ln -s /rw/config/buskill.rules /etc/udev/rules.d/ sudo udevadm control --reload ``` Now, let\'s add a new udev \'`.rules`\' file. This one will always *just* lock your screen, and it\'s what will be put in-place when BusKill is \"disarmed\". Execute the following on your \'`sys-usb`\' Qube: ``` cat << EOF | sudo tee /rw/config/buskill.lock.rules ################################################################################ # File: sys-usb:/etc/udev/rules.d/buskill.rules -> /rw/config/buskill.lock.rules # Purpose: Just lock the screen. For more info, see: https://buskill.in/qubes-os/ # Authors: Michael Altfield # Created: 2023-05-10 # License: GNU GPLv3 ################################################################################ ACTION=="remove", SUBSYSTEM=="usb", ENV{ID_MODEL}=="Micromax_A74", RUN+="/usr/bin/qrexec-client-vm dom0 buskill.lock" EOF ``` The careful reader will see that we\'re not *actually* disarming BusKill in the same sense as our [BusKill GUI app](https://github.com/buskill/buskill-app/). Indeed, what we\'re *actually* going to do is swap these two files for 30 seconds. This way, if BusKill is armed and you remove the cable, your computer shuts-down. But if you want to disarm, the procedure becomes: 1. Hit the \"Disarm BusKill\" keyboard shortcut (see below) 2. Wait for the toast popup message indicating that BusKill is now disarmed 3. Remove the cable within 30 seconds 4. Your screen locks (instead of shutting down) Personally, I can\'t think of a QubesOS user that would want to leave their machine unlocked when they go to the bathroom, so I figured this approach would work better than an *actual* disarm. Bonus: when you return from your break, just plug-in the BusKill cable in, and it\'ll already be armed (reducing the risk of user error due to forgetting to arm BusKill). Now, let\'s add the actual \'`buskill-disarm.sh`\' script to disarm BusKill: Execute the following on your \'`sys-usb`\' Qube: ``` cat << EOF | sudo tee /usr/local/bin/buskill-disarm.sh #!/bin/bash ################################################################################ # File: sys-usb:/usr/local/bin/buskill-disarm.sh # Purpose: Temp disarm BusKill. For more info, see: https://buskill.in/qubes-os/ # Authors: Tom # Co-Auth: Michael Altfield # Created: 2023-05-10 # License: GNU GPLv3 ################################################################################ # replace the 'shutdown' trigger with the 'lock' trigger sudo rm /etc/udev/rules.d/buskill.rules sudo ln -s /rw/config/buskill.lock.rules /etc/udev/rules.d/buskill.rules sudo udevadm control --reload # let the user know that BusKill is now temporarily disarmed notify-send -t 21000 "BusKill" "Disarmed for 30 seconds" -i changes-allow # wait 30 seconds sleep 30 # replace the 'lock' trigger with the 'shutdown' trigger sudo rm /etc/udev/rules.d/buskill.rules sudo ln -s /rw/config/buskill.rules /etc/udev/rules.d/buskill.rules sudo udevadm control --reload notify-send -t 5000 "BusKill" "BusKill is Armed" -i changes-prevent EOF sudo chmod +x /usr/local/bin/buskill-disarm.sh ``` ## dom0 If you followed our [previous guide to setting-up BusKill in QubesOS](/qubes-os/), then you shouldn\'t need to add any files to dom0. What you *do* need to do is setup some keyboard shortcuts. In the QubesOS GUI, click on the big `Q` \"Start Menu\" in the top-left of your XFCE panel to open the Applications menu. Navigate to \'`System Tools`\' and click Keyboard | [](https://buskill.in/qubes-disarm) | [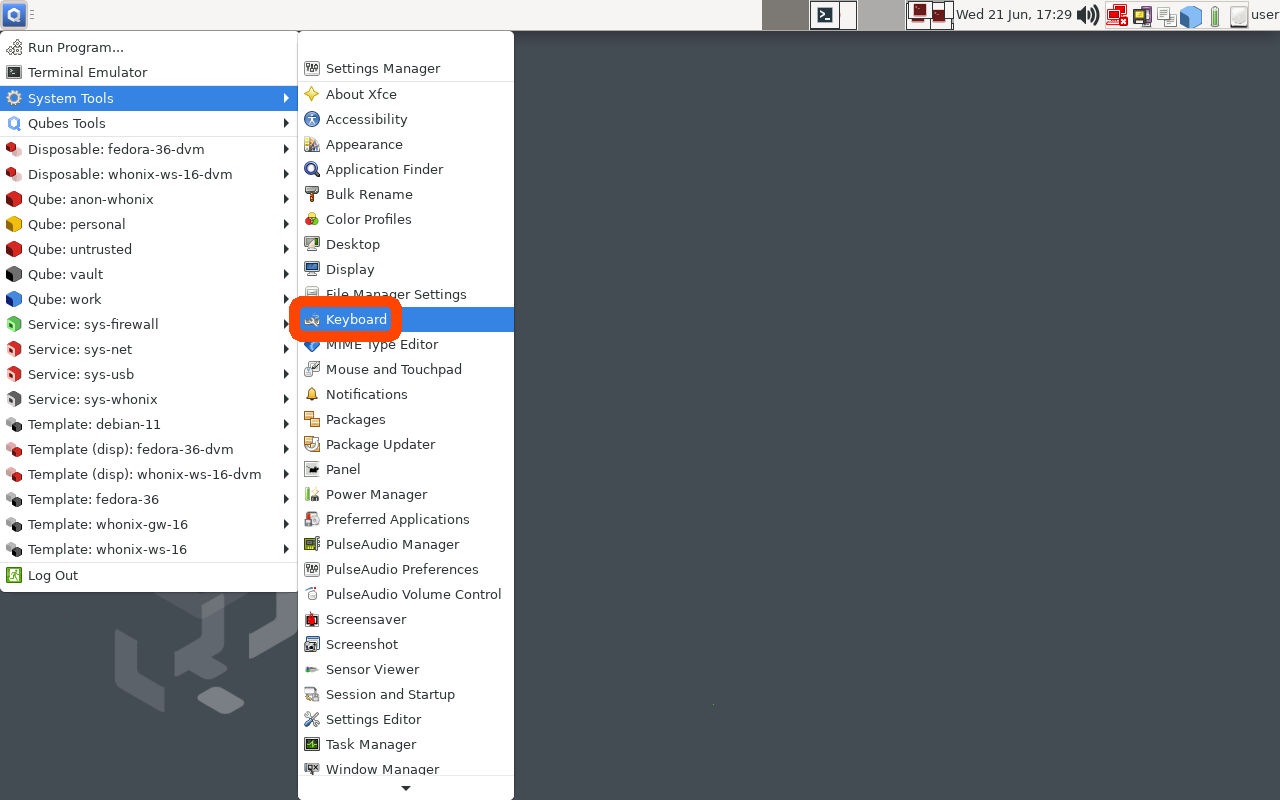](https://www.buskill.in/qubes-disarm/) | |:--:|:--:| | Click the “Q” to open the QubesOS Application Menu | Click System Tools -> Keyboard | Click the \'`Application Shortcuts`\' Tab and then click the \'`+ Add`\' button on the bottom-left of the window. | [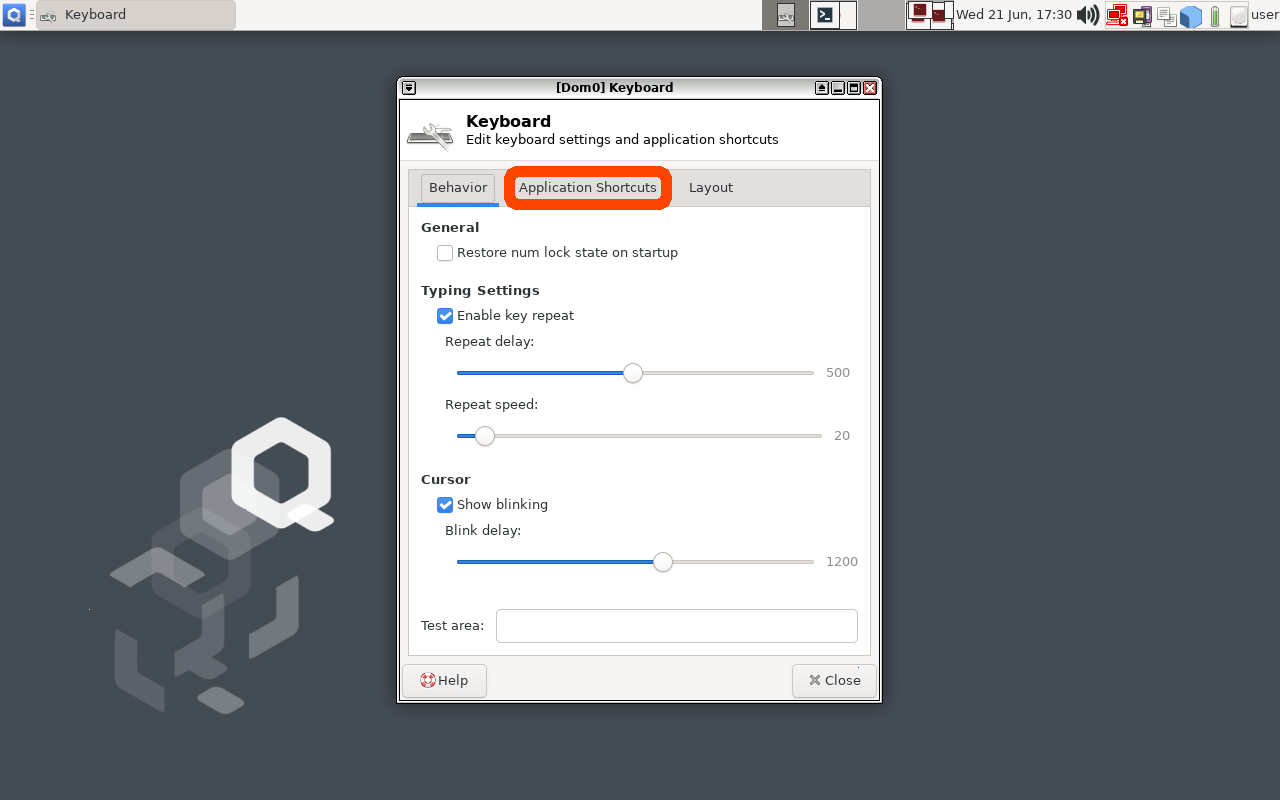](https://www.buskill.in/qubes-disarm/) | [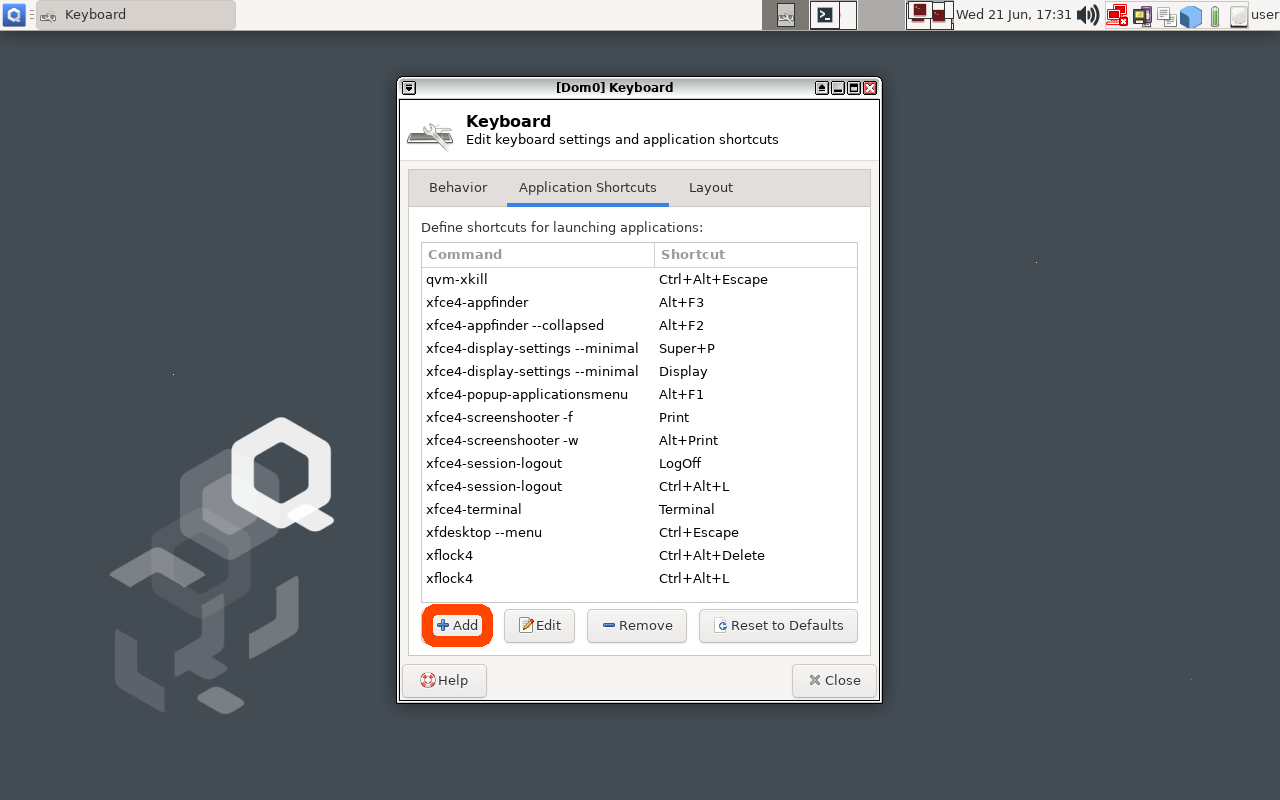](https://www.buskill.in/qubes-disarm/) | |:--:|:--:| | Click the “Application Shortcuts” tab to add a Keyboard Shortcut in Qubes | Click the “Add” Button to add a new Keyboard Shortcut in Qubes | In the \'`Command`\' input field, type the following ``` qvm-run sys-usb buskill-disarm.sh ``` The above command will execute a command in \'`dom0`\' that will execute a command in \'`sys-usb`\' that will execute the \'`buskill-disarm.sh`\' script that we created above. | [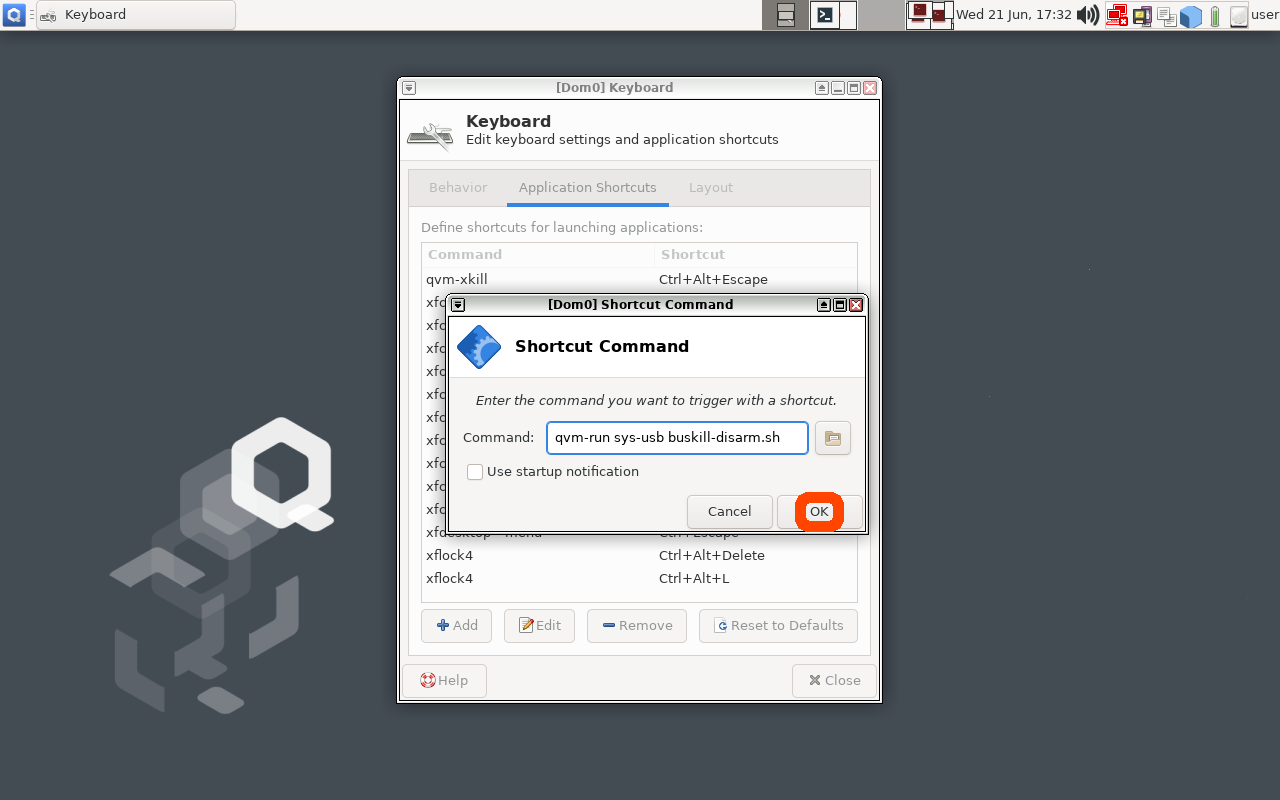](https://www.buskill.in/qubes-disarm/) | |:--:| | After typing the command to be executed when the keyboard shortcut is pressed, click the \"OK\" button | Now click \"OK\" and, when prompted, type Ctrl+Shift+D (or whatever keyboard shortcut you want to bind to \"Disarming BusKill\"). | [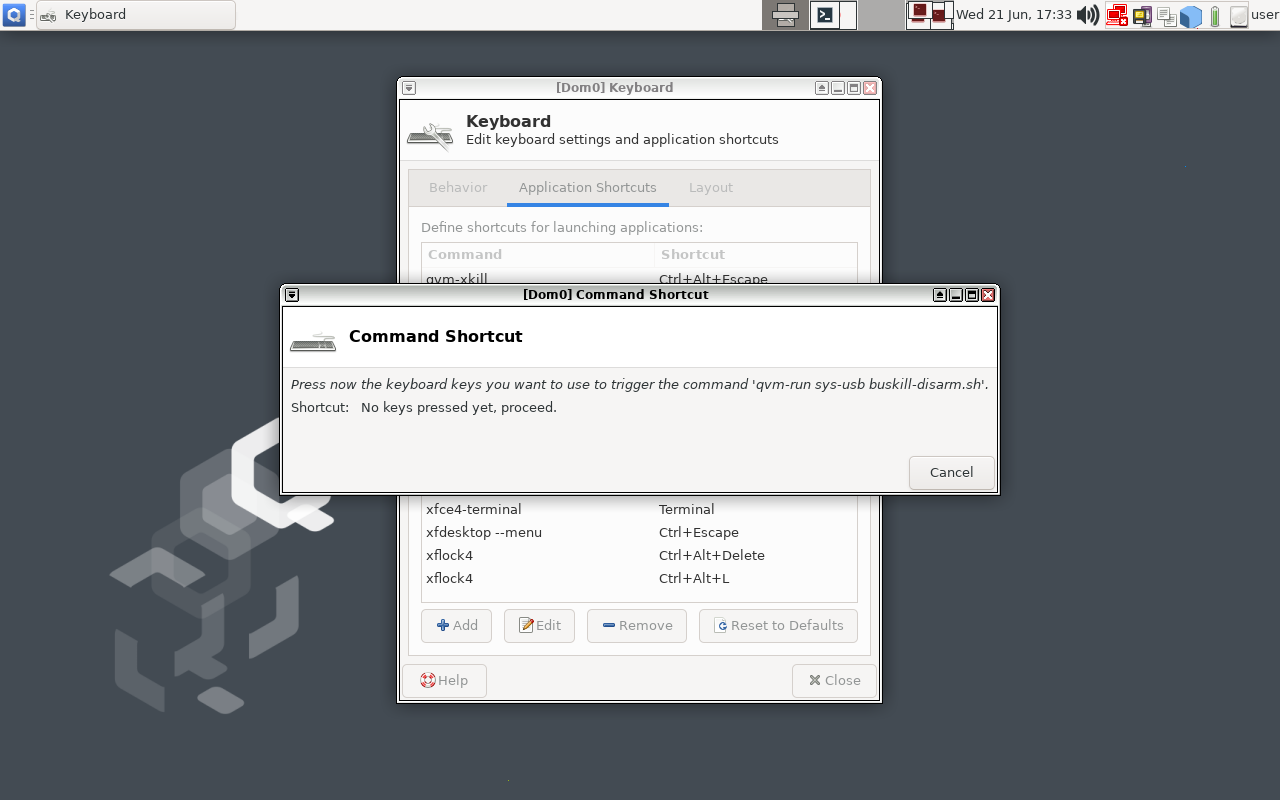](https://www.buskill.in/qubes-disarm/) | [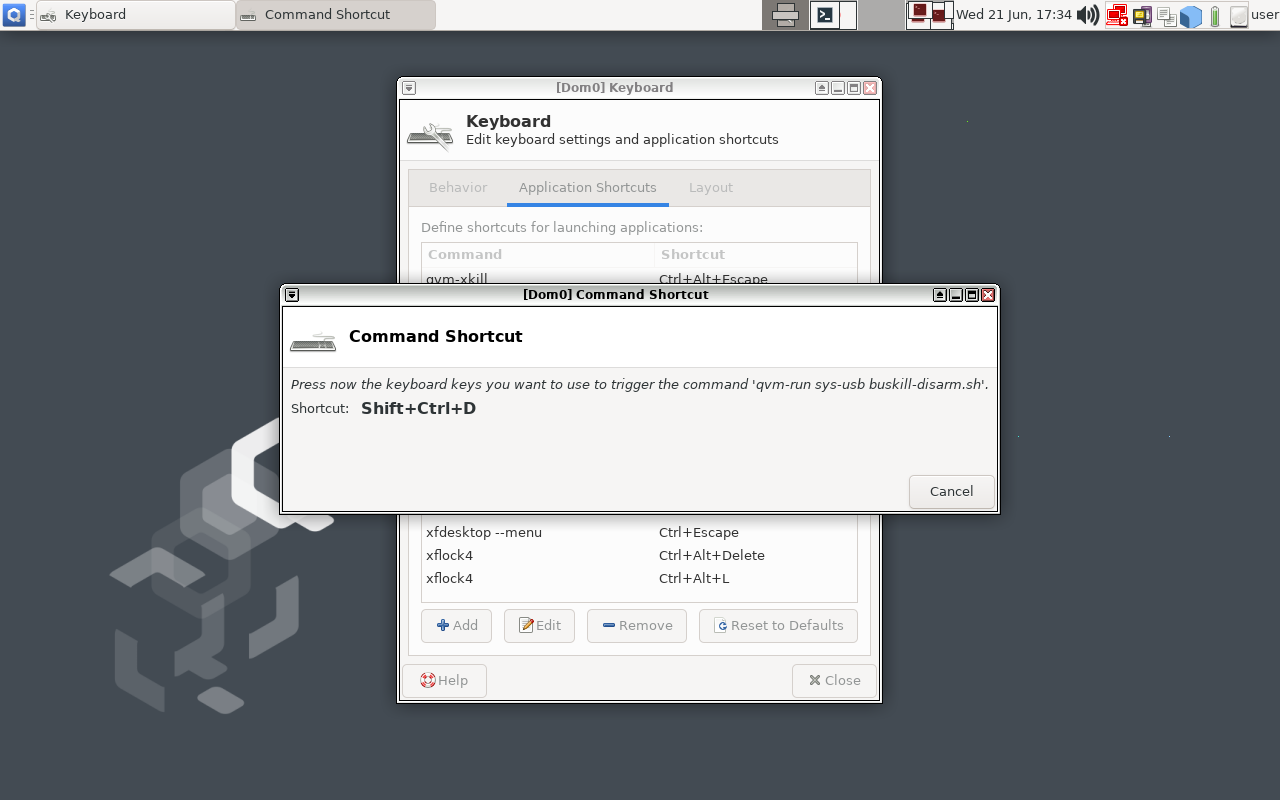](https://www.buskill.in/qubes-disarm/) | |:--:|:--:| | Type "Ctrl+Shift+D" or whatever keyboard shortcut you want to trigger BusKill to be disarmed for 30 seconds | | You should now have a keyboard shortcut binding for disarming BusKill! [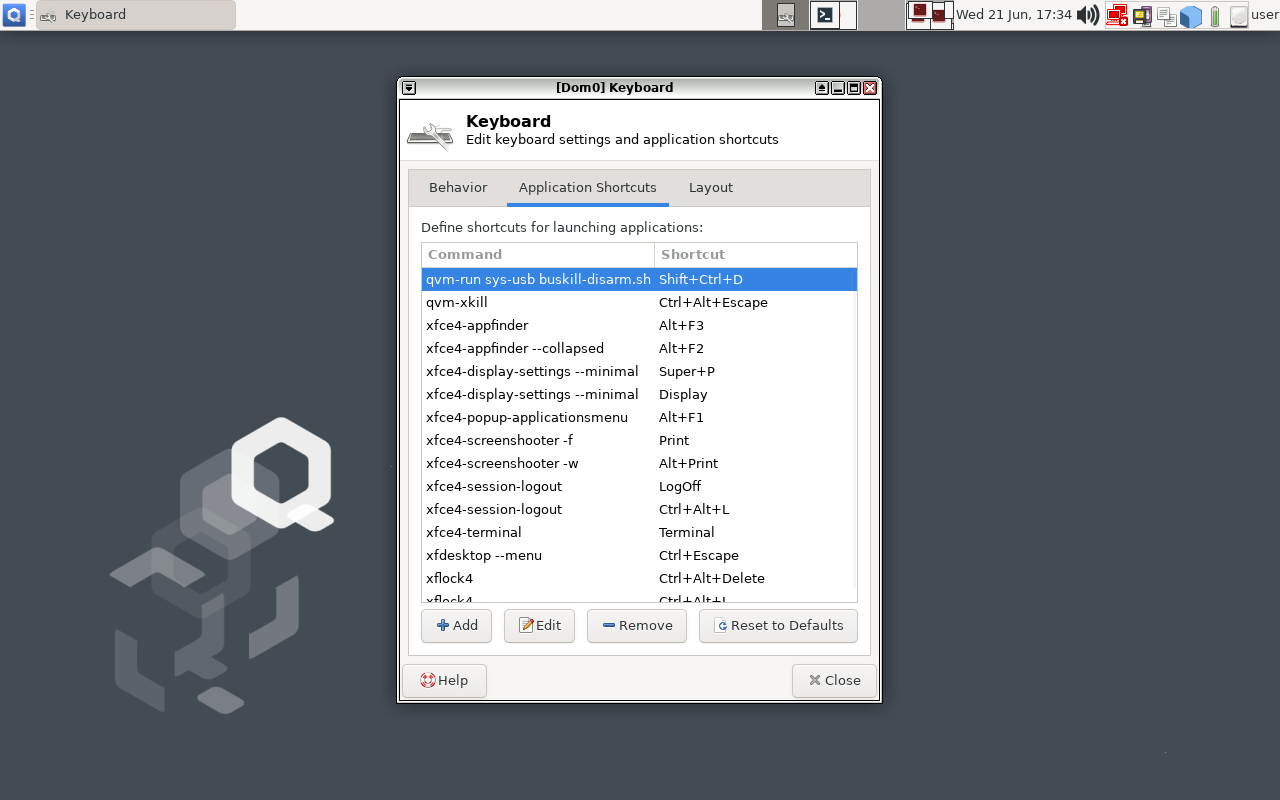](https://www.buskill.in/qubes-disarm/) # Test It! At this point, you can test your new (temporary) BusKill Disarm functionality by: 1. Plugging-in your BusKill cable 2. Typing Ctrl+Shift+D 3. Waiting for the toast popup message to appear indicating that BusKill is disarmed for 30 seconds 4. Unplugging your BusKill cable Your machine should lock, not shutdown. | [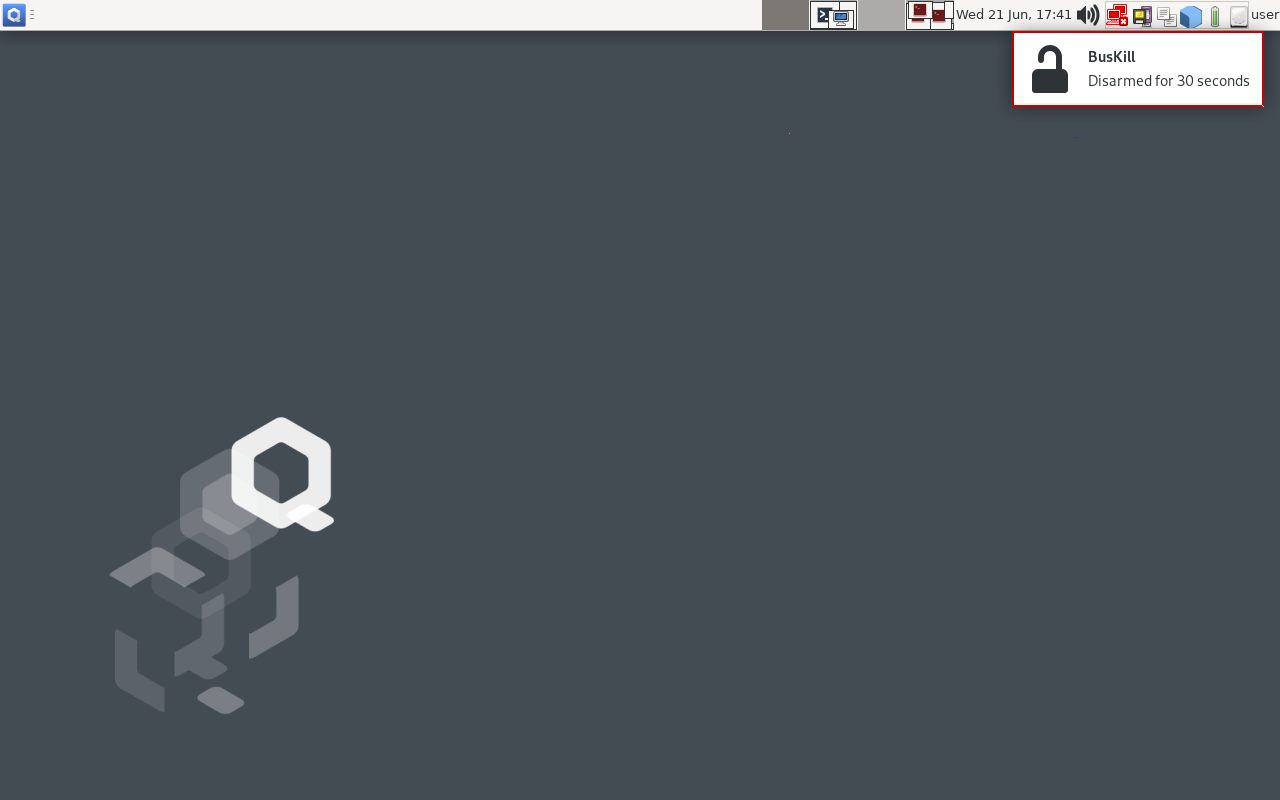](https://www.buskill.in/qubes-disarm/) | |:--:| | After hitting the keyboard shortcut to disarm BusKill, you have 30 seconds to remove the cable | After 30 seconds, return to your computer and test the normal \"arm\" functionality: 1. Plug-in your BusKill cable 2. Unlock your screen 3. Unplug your BusKill cable Your computer should shutdown, not lock. | [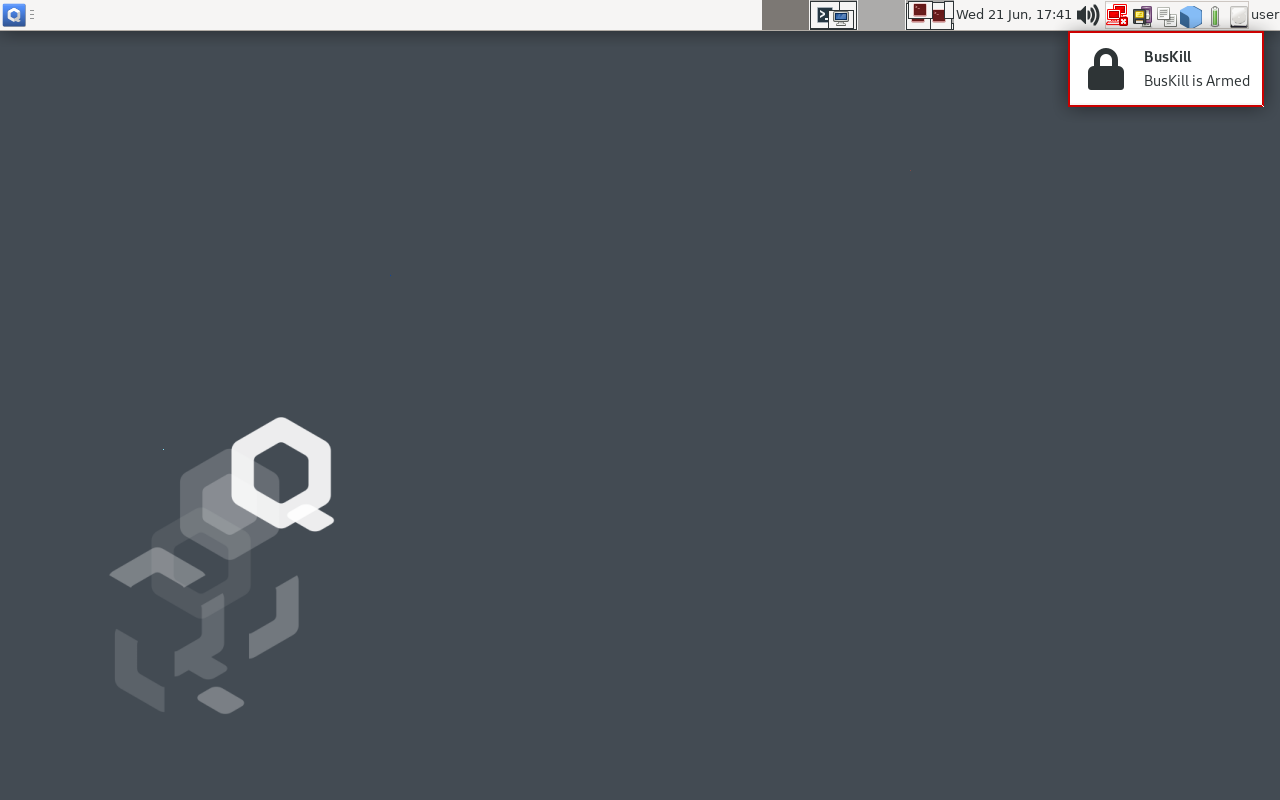](https://www.buskill.in/qubes-disarm/) | |:--:| | 30 seconds after hitting the keyboard shortcut, BusKill will arm itself | # Troubleshooting Is unplugging your USB device doing nothing? Having other issues? See the [Troubleshooting section](https://buskill.in/qubes-os/#troubleshooting) in our original guide to using BusKill on QubesOS. # Limitations/Improvements Security is porous. All software has bugs. Nothing is 100% secure. For more limitations to using BusKill on QubesOS, see the [Limitations section](https://busill.in/qubes-os/#limitations) in our original guide to using BusKill on QubesOS. # Buy a BusKill Cable We look forward to continuing to improve the BusKill software and making BusKill more accessible this year. If you want to help, [please consider purchasing a BusKill cable](https://buskill.in/buy) for yourself or a loved one. It helps us fund further development, and you get your own BusKill cable to keep you or your loved ones safe. You can also buy a BusKill cable with bitcoin, monero, and other altcoins from our [BusKill Store's .onion site](http://buskillvampfih2iucxhit3qp36i2zzql3u6pmkeafvlxs3tlmot5yad.onion/buy/). Stay safe, The BusKill Team https://www.buskill.in/ http://www.buskillvampfih2iucxhit3qp36i2zzql3u6pmkeafvlxs3tlmot5yad.onion
TIL [the French government may have broken encryption on a LUKS-encrypted laptop](https://nantes.indymedia.org/posts/87395/une-lettre-divan-enferme-a-la-prison-de-villepinte-perquisitions-et-disques-durs-dechiffres/) with a "greater than 20 character" password in April 2023. * https://nantes.indymedia.org/posts/87395/une-lettre-divan-enferme-a-la-prison-de-villepinte-perquisitions-et-disques-durs-dechiffres/ When upgrading TAILS today, I saw their announcement changing LUKS from PBKDF2 to Argon2id. * https://tails.boum.org/security/argon2id/index.en.html The release announcement above has some interesting back-of-the-envelope calculations for the wall-time required to crack a master key from a LUKS keyslot with PBKDF2 vs Argon2id. And they also link to Matthew Garrett's article, which describes [how to manually upgrade](https://mjg59.dreamwidth.org/66429.html) your (non-TAILS) LUKS header to Argon2id. * https://mjg59.dreamwidth.org/66429.html
 webdesigneracademy.com
webdesigneracademy.com
From the moment I began my freelance web design business back in 2014, I was collecting payments via Stripe and happily paying their processing fees for the ability to grow my business from just a desire for more freedom to running a company that employs women and supports them to create their own freedom and financial independence. It never occurred to me that using Stripe to process payments would become one of the biggest risks to my small business. My Stripe account was hacked due to Stripe’s lax security, over $70,000 of fraudulent charges were processed by the hacker through a fake connected account, paid out instantly to that person via Stripe’s Instant Payments to the hacker’s pre-paid debit card, and Stripe started pulling the money out of my business bank account to pay back the victims of the theft. And Stripe says it’s my fault that my account was hacked and that I’m liable to pay back the victims of the fraud. Listen to the full podcast episode or read on to find out exactly what happened and how to protect your business. ______________________ On a quiet Monday morning after the Easter holiday, I was sipping coffee on my couch in Columbus, Ohio like I normally do, snuggling with my dog and going through my normal morning entrepreneurial routine of checking emails and DMs on my business account when I see an email from Stripe with the subject line: “Subject: [Action required] Closure of your Stripe account” We recently identified payments on your Stripe account that don’t appear to have been authorized by the customer, meaning that the owner of the card or bank account didn’t consent to these payments. As a precautionary measure, we will no longer accept payments for [your company]. We will also begin issuing refunds on card payments on April 15, 2023, although they may take longer to appear on the cardholder’s statement. Please refer to your dashboard for a list of the charges that will be refunded. If there are insufficient funds on your account to cover any refunds, those refunds won’t be processed and any outstanding funds will remain in your account . If you believe that we’ve misunderstood or miscategorized your business and would like us to conduct another review of your account , please complete the form on your Stripe Dashboard to provide more information about your business. Request further review If you have any questions, you can contact us any time from our support site.” I remember thinking… yeah, this is probably some phishing scam… So I check out the “From” address, and actually click into it to see the actual address and it’s saying it’s FROM accounts@stripe.com… And I log into my Stripe account from a separate browser, you know, just in case… and after using my Authenticator app because I have 2-factor authentication set up on my account, I see the request at the top of my account asking me to provide proof that I am the owner of my business. I look at my recent authorized transactions and nothing is out of the ordinary… all of the successful payment listed are from students inside my Web Designer Academy who have been making their monthly membership payments like clockwork. And I think, “This must just be a mistake. I’ve been a customer of Stripe for 8 years now. I’ll submit all the documentation Stripe requested and I’m sure that will take care of it.” So I grab my laptop, submit all the documentation right away, and get back to snuggling and scrolling. Then I log into my back account and see a withdrawal from my business checking account from Stripe for over $600. And another pending transaction for a withdrawal over $2000. And no credits for the payments that were made by students over the weekend. And I’m feeling very confused thinking, “What is happening?” I’m starting to feel the anxiety bubbling up, but I tell myself to be patient. Once they review all the documents I submitted to prove that I am who I say I am, this will all get resolved. A few hours later, I receive another email: “Subject: Additional review completed for Stripe Shop” Whew, I think. I’m glad they took care of this so quickly. I click into the email, and my heart starting pounding in my chest as I read it: “Thank you for providing additional information about your business. After reviewing your account again, we’ve confirmed that your business represents a higher risk than we can currently support. We are unable to accept payments for [your company] moving forward. Payouts to your bank account have been paused, and we will issue refunds on any card payments by May 10, 2023, although they may take longer to appear on the cardholder’s statement. If there are insufficient funds on your account to cover any refunds, these refunds will not be processed and any outstanding funds will remain on your account. Please refer to your Dashboard for a list of the charges to be refunded. If you’d like to further appeal our decision, please contact us.” I can feel the panic rising in my body. I tap on the Stripe app on my phone and I see that there’s a negative payout balance… but all the transactions listed in the app are legit. I logged back into my Stripe account via my computer trying to figure out what in the world they are talking about, what are all these charges that they are saying are fraudulent? I’m looking for a phone number I can call to talk to someone. I start clicking through every link in my Stripe dashboard, and when I get to the “Connect” menu item, that’s when I see it. Two accounts with the business name of “Netflix.com” under the name “Albert Dawkins” which between the two accounts had racked up over $70,000 in credit card charges in the 3 days over the Easter holiday weekend. Looking more closely, the ill-gotten gains were paid out instantly to a pre-paid debit card via Stripe’s Instant Payouts feature the moment the transactions were successful. I realized my Stripe account was hacked. ...
netsec - Network Security
!netsec@discuss.tchncs.deThis is the netsec Community, a community-curated aggregator of technical information security content. Our mission is to extract signal from the noise - to provide value to security practitioners, students, researchers, and hackers everywhere.
Content Guidelines:
- Content should focus on the "How".
- Always try to link to the original source.
- Titles should provide context.
- Ask Questions with a "[Question]" prefix in the Title.
- Hiring Posts must go in the [Hiring] (stickied) Threads.
- Commercial advertisement is discouraged.
Discussion Guidelines:
- Don't create unnecessary conflict.
- No trolling allowed, limit the use of jokes and memes.
- Don't complain about content being a PDF.
- Be nice to each other, everybody started somewhere.
Prohibited Content:
- No populist news articles (CNN, BBC, FOX, etc)
- No curated lists.
- No social media posts (Facebook, Twitter, etc).
- No image-only/video-only posts.
- No livestreams.
- No Tech Support requests.
- No paywalled/regwalled content (use archive.is if possible?)
- No commercial advertisement.
- No crowdfunding posts.
- No personally identifiable information.
- No doxxing, and no harrassment of any kind.